Chapter 10. Cloud Technologies
10.6 Site-to-Site VPN between FortiGate on Premise and FortiGate in the AWS
Learning Objectives
- Configure a VPN Wizard in AWS
- Configure site-to-site VPN between FortiGate on premise and AWS
- Identify FortiGate subnets in AWS

Scenario: In this lab, we are going to create a site-to-site VPN from FortiGate on premise to FortiGate in the AWS. Knowing the configuration of section 10.5 is necessary for this lab. Port1 FortiGate on premise is set as a DHCP, so it will receive an IP address from Cloud.
On-Premise FortiGate Configuration
| Device | Interface | IP address |
|---|---|---|
| FortiGate | Port 1 | DHCP Client |
| Port 2 | 192.168.10.1/24 | – |
| WebTerm | Eth0 | 192.168.10.2/24 |
- Configure the interfaces of the firewall. Port2 by default is an internal interface and named “LAN” and Port1 is an external interface and named “WAN”.
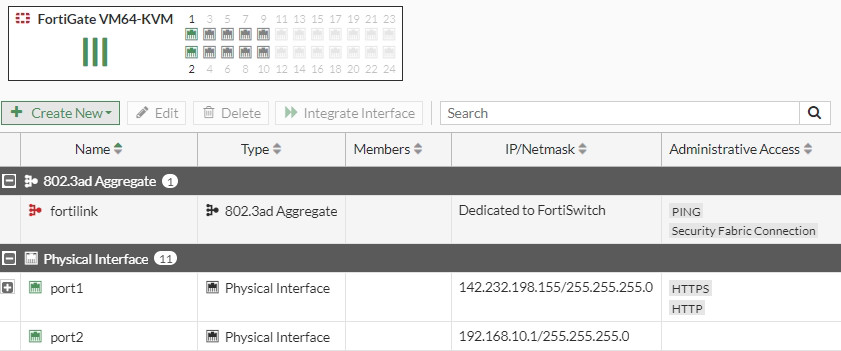
Figure 10.155: Firewall interfaces - Create a site-to-site VPN from IPsec Wizard as Figures 10.156 to 10.158.
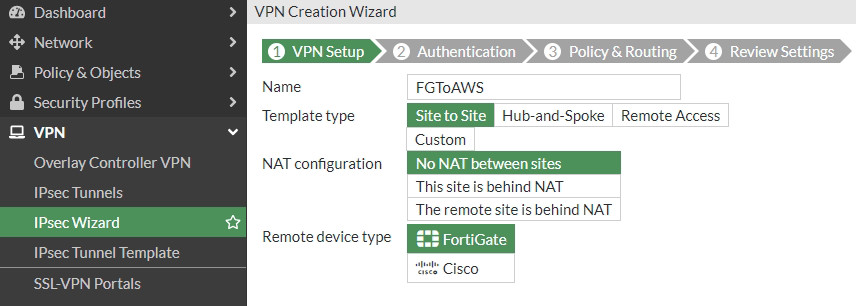
Figure 10.156: Select VPN name 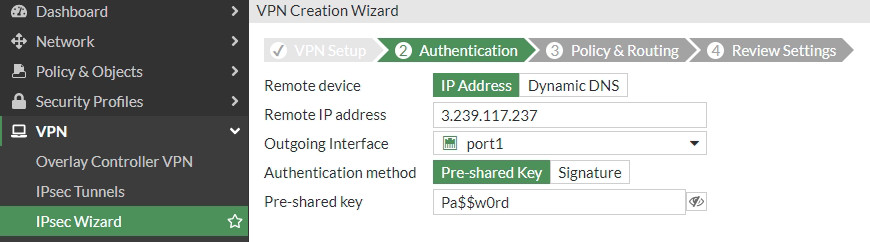
Figure 10.157: Set remote IP address 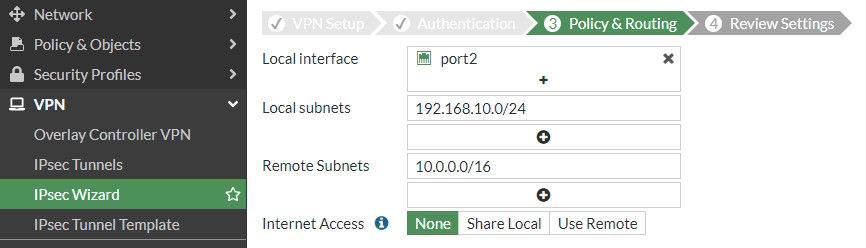
Figure 10.158: Set Policy & Routing - Create a static route to the default gateway.
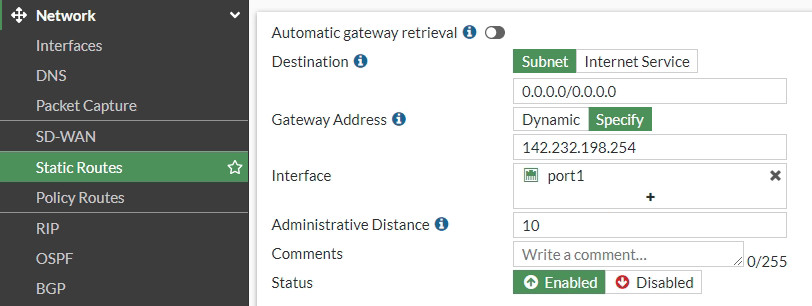
Figure 10.159: Set a default gateway
AWS Configuration
- Create a FortiGate firewall in AWS and configure the interfaces. You need to do all steps in section 10.5.
- Create a VPN from IPsec Wizard as Figures 10.160 to 10.162.
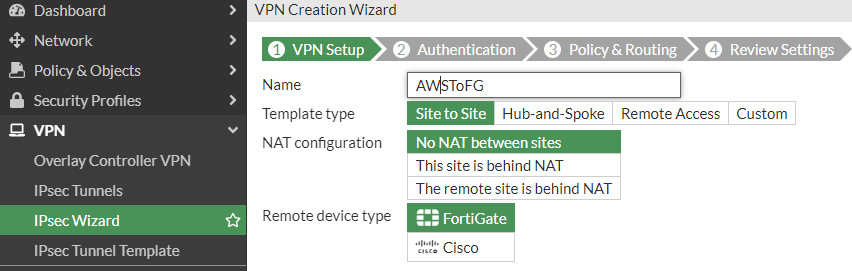
Figure 10.160: Select VPN name 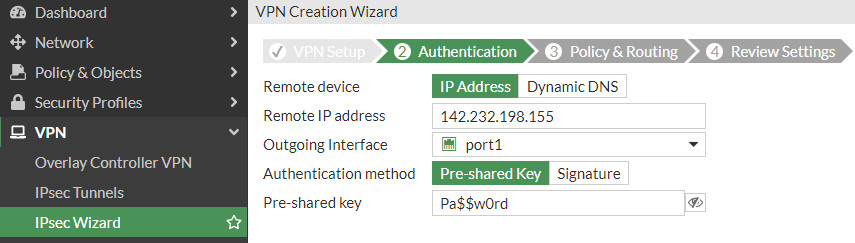
Figure 10.161: Set a remote IP address 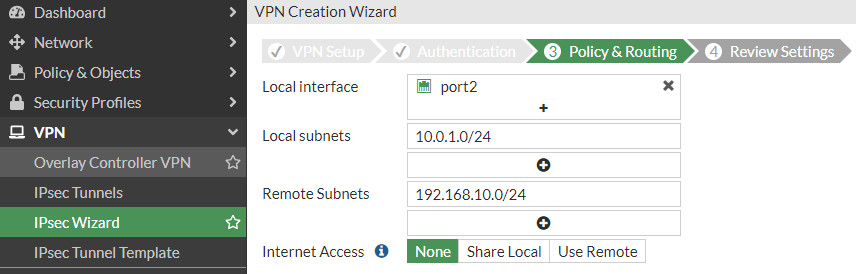
Figure 10.162: Set Policy & Routing - Create static routes on FortiGate. We are going to create two static routes as follows:

Figure 10.163: Set a default gateway via 10.0.0.1 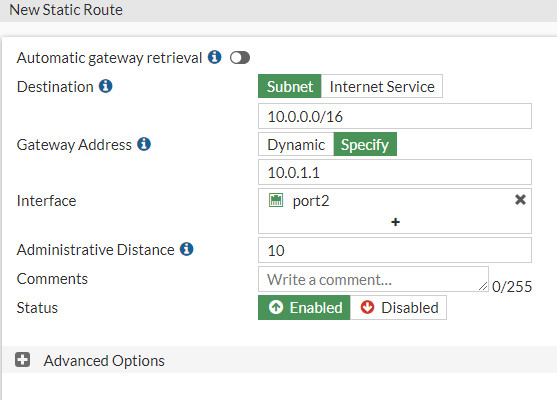
Figure 10.164: Create a static route to 10.0.0.0/16 network via 10.0.1.1 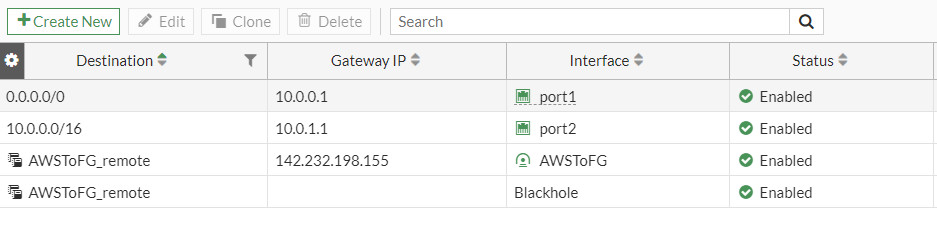
Figure 10.165: Overview of static routes on FortiGate - Go to VPN > IPsec Tunnels and check status of the tunnel.
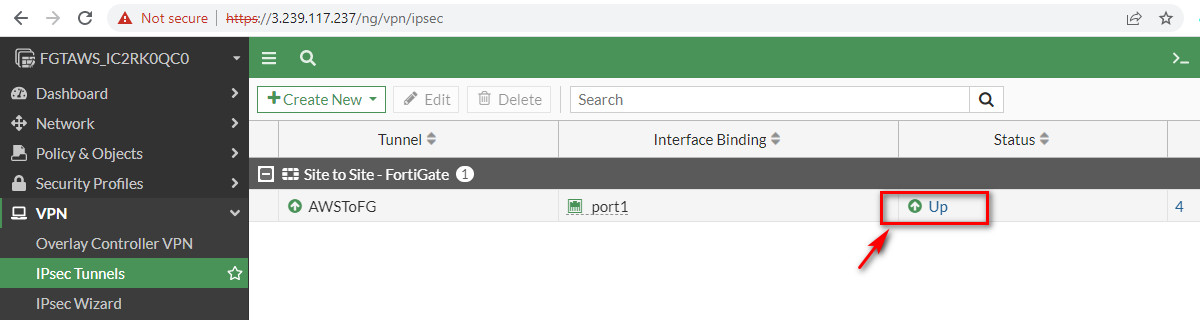
Figure 10.166: Check the status of the tunnel on AWS 
Figure 10.167: Check status of tunnel on FortiGate on premise - You should be able to ping from WebTerm to Virtual Machine on AWS and vice versa.
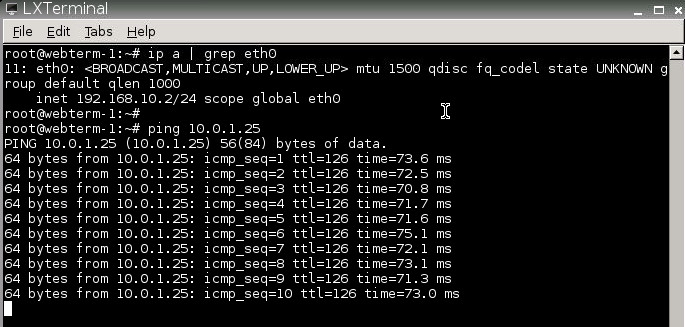
Figure 10.168: Ping from WebTerm to Windows VM 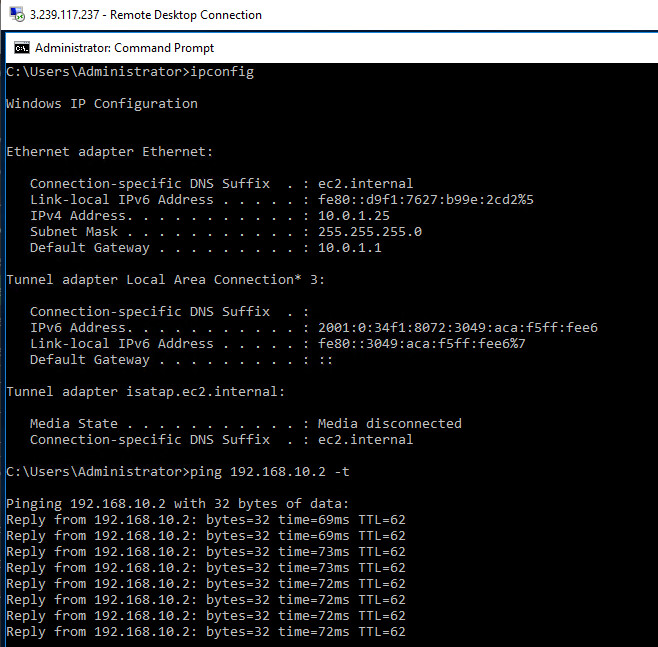
Figure 10.169: Ping from Windows VM to WebTerm