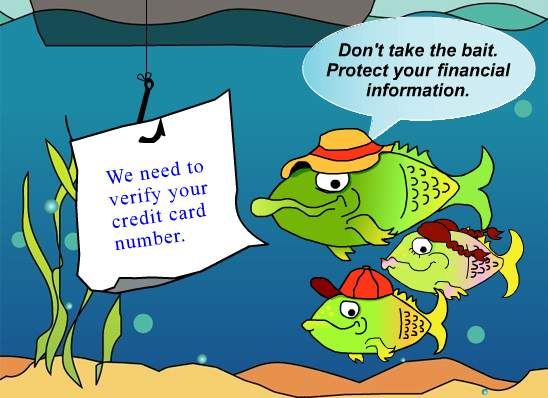
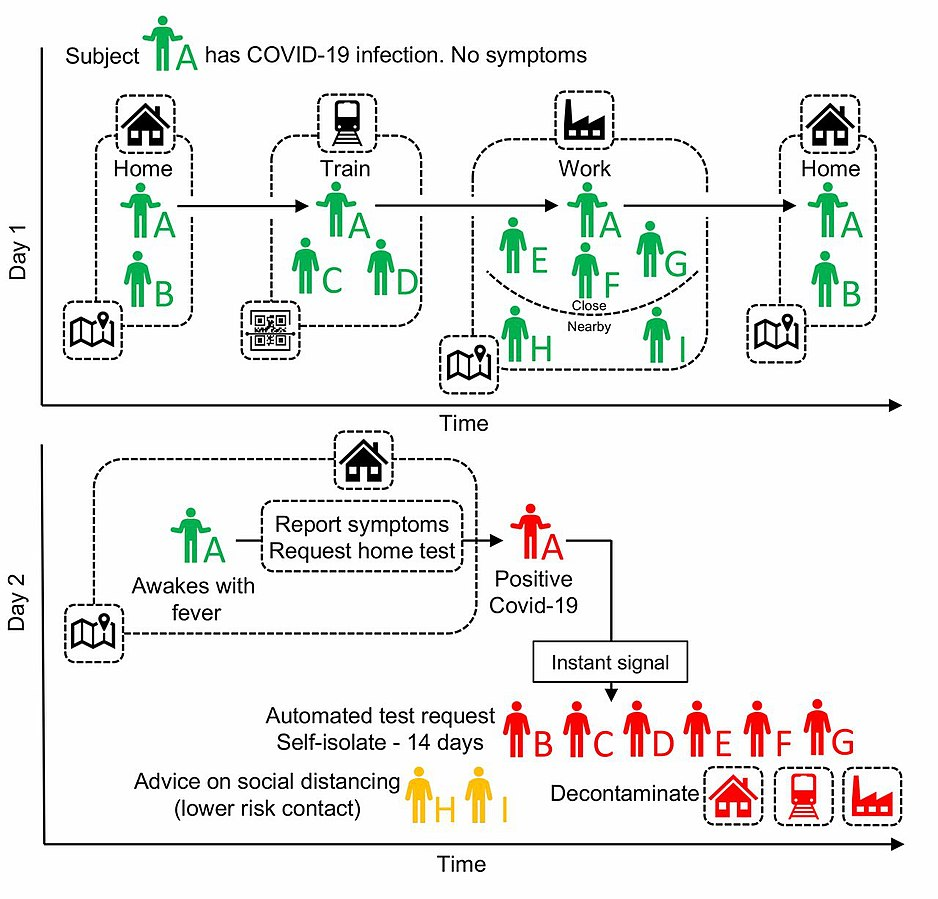
Figure 8.1 Managing your privacy and online presence
Some companies provide us with free access to things like email, social media, etc. in exchange for showing us advertising. These companies are interested in knowing as much as possible about us (e.g. gender, age, income, etc.) in order to show us advertising that is targeted to our particular demographic. This collection of our personal information can be either seen as intrusive, or as useful (since the ads are more relevant), or somewhere in between. There is information we can purposely put online for others, and then there is information we can inadvertently leave behind when we do things such as search the web. You will want to make a conscious decision as to how to balance your online presence with your privacy. There are a number of factors that impact your online privacy and presence.
Web Browsing Privacy
Browser Cookies
Web browser cookies are a small text file that records information about your visit to a web site. The next time you return to the web site, the browser reads the cookie file. Similar to a fortune cookie, a browser cookie contains a small amount of text or a message. A few facts about cookies:
- Cookies aren’t malicious, they can’t harm your computer like malware potentially could.
- Cookies’ primary purpose is customization of web pages the next time you interact with or return to the site.
- Cookies can’t steal information about you, they only know what you do on the website or what you tell them.
- For example, if on a website you look at a web page selling a particular pair of shoes, a cookie can remember that.
- If the web site asks for you to type your name or a username, it can remember that. Cookies don’t have the ability to look at other files on your computer to try and figure out what your name is, so if the web site knows your name, you must have told the website this information.
- Cookies are only read by the website that created them, so in theory they weren’t designed to share information between websites (website developers found a clever way around this – third party cookies)
First and Third Party Cookies
- First party cookies are created by the website you set out to visit.
- Third party cookies are created when the website you visit temporarily redirects you to a cookie tracking website.
- If you visit another web site that uses the same third party cookie tracking website, then information effectively passes from one web site to the other. This is how, for example an advertisement for the clothing you were looking at buying on one web site shows up in an advertisement on a different website that you look at.
- Third party tracking cookies are considered a privacy issue, and government legislation has made many websites obtain your consent before they use a cookie on a site you visit.
- Third party tracking cookies are on the way out. The Safari and Firefox web browsers started blocking them in 2020, and the Chrome browser will also phase them out by 2022.
Clearing Your Browsing History
When you browse the web, your web browser keeps certain information:
- Cache. The browser cache keeps images and text from web pages you have recently visited. It’s primary purpose is to make your web browsing faster. If you revisit a web page you have recently visited, the browser will pull web page information from the cache, rather than going to the website to get it. It’s faster to retrieve information from the cache than from the Internet, so having a cache speeds up the browsing experience.
- History. Your browser history is a list of websites that you have visited. When you start typing the address of a website, you may see suggestions as to what website you may want, your browser history is playing a part in generating these suggestions – it assumes if you have been to a site once, you may want to go back again.
- Cookies. As previously discussed, a cookie is a small text file that records information about your visit to a web site, such as your username and/or pages you looked at.
Why would I want to clear my browser history?
You might have been using a computer other than your own (e.g. coffee shop, library), and for privacy reasons, you might want to clear your history. Another reason could be if a web page you have previously visited isn’t loading properly, clearing the history may solve that problem. In general, if you have your own device (phone, tablet, laptop), most people don’t bother clearing their browser history.
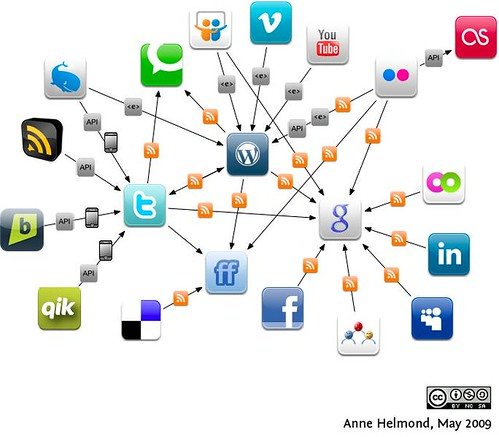
How do I clear my browser history?
In your browser (e.g. Firefox, Safari, Chrome, Edge, etc.) there typically is a “settings” menu, and somewhere in that menu will be the option to clear the history. To get the specific steps for your particular browser, search for the words “clear browser history” and add the name of your browser to the search.
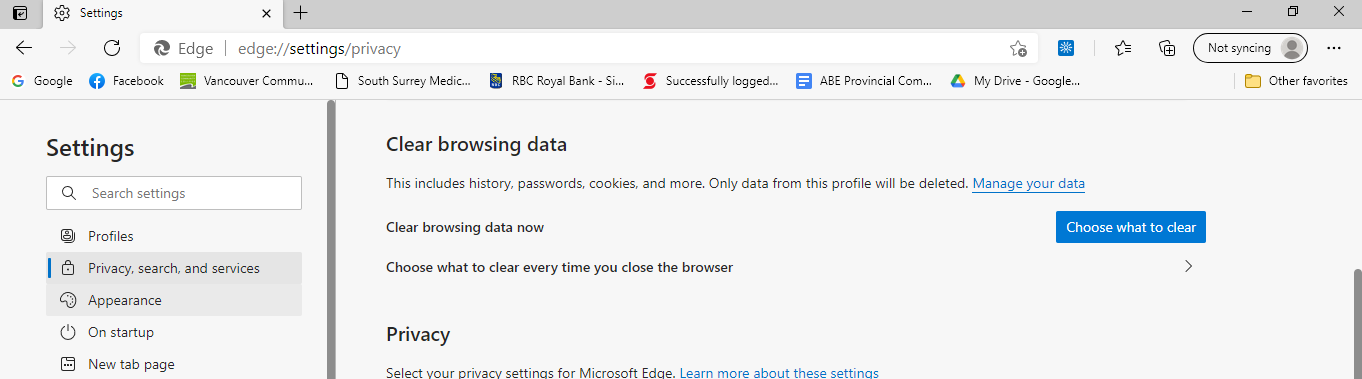
Figure 8.2 edge://settings/privacy
What happens when my browser history is cleared?
Depending on your browser, you may need to select each of the three main areas to clear, or they may be cleared in a single step. Here’s what to expect if you clear each of the areas:
- Cache. If you have a slower Internet connection, it may look like your browser is a bit slower than it used to be until the cache is rebuilt.
- History. Initially, you won’t see the most relevant autocomplete suggestions of sites you may want to visit, but your history will rebuild itself over time.
- Cookies. For any websites that you had chosen “remember me”, you will likely need to put in your username again the next time you log into the site again.
Private Mode in Web Browsers
So what if you would like to visit a particular website and don’t want that website as part of your browsing history, but you don’t want to clear your entire browsing history? Perhaps you are on your lunch break at work, and don’t want the details of your visit to an online shopping site recorded by the browser. The way to accomplish this is to switch to your browser’s “private” browsing mode. Different browsers have slightly different names for their private browsing mode:
Table 8.1 Private Browsing Labels | Browser | Name for Private Browsing |
|---|
| Firefox | Private |
| Chrome | Incognito |
| Safari | Private |
| Edge | InPrivate |
Generally speaking, for each of these browsers look for three dots, three lines or a new window tab near the top right corner of the browser, clicking on this will open a menu, and then you can open a new window in a private browsing mode.
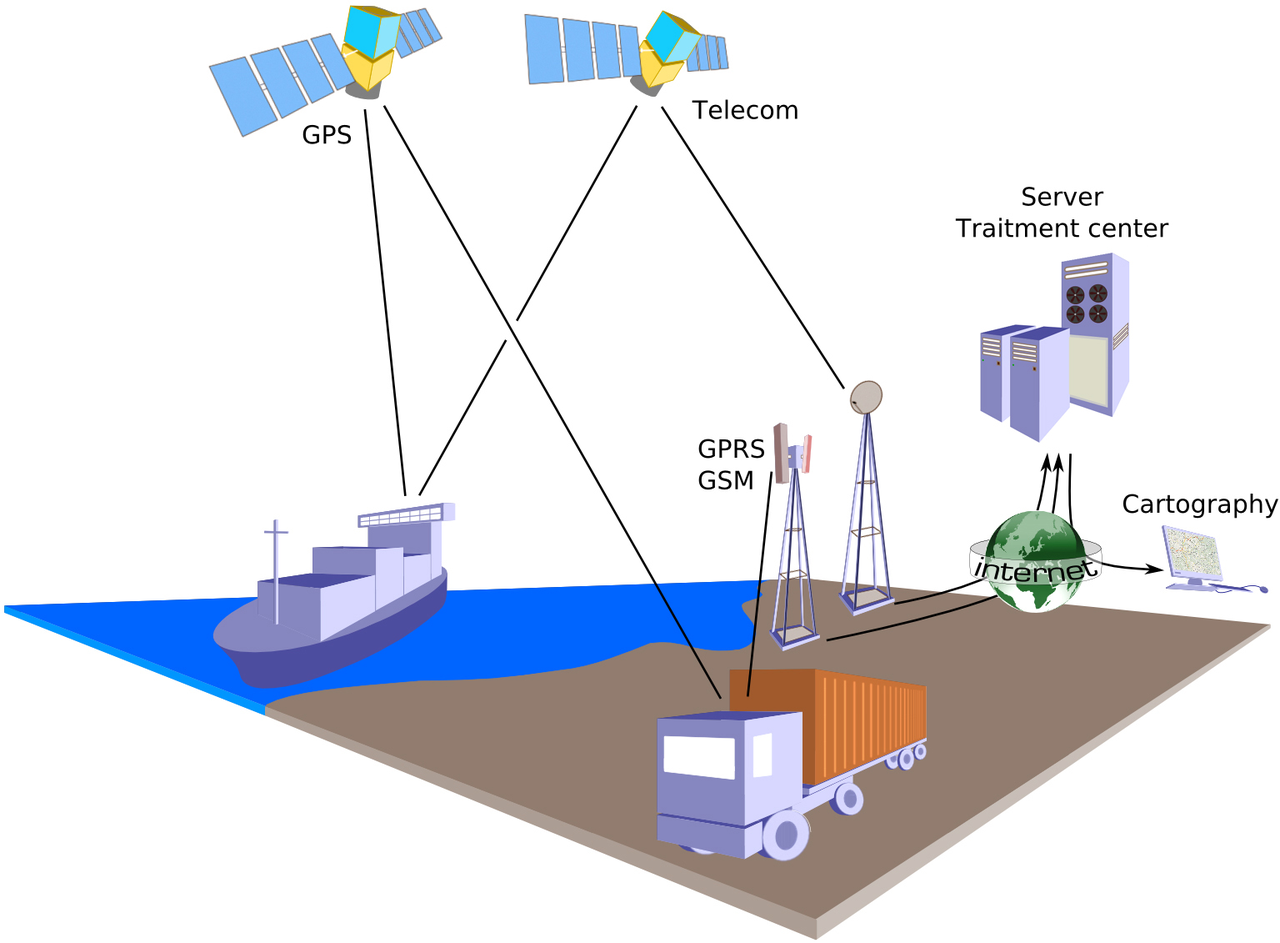
Private Browsers
The private browsing mode in the popular browsers provides some extra security in that your web history is not saved on the computer you are using; however, your IP address is still trackable (which can be traced – with some effort – to your physical location). If you want an extra level of anonymity, you could download a special browser for this purpose, such as Tor or Brave. These browsers not only hide your history, they mask your IP address and physical location from the websites you visit by routing your browsing through several servers before it reaches your destination. These connections are also encrypted to increase anonymity.
VPNs (Virtual Private Networks)
Some people use a VPN provider to enhance online privacy. Websites know the IP (Internet Protocol) address of people who visit the website. An IP address has an associated real world location. You can visit a website such as What Is My IP Address and see your IP address, as well as your approximate location on a map.
VPNs act as an intermediary between you and the website you visit, so the website sees the VPN’s IP address, rather than seeing your IP address. So once your VPN connection is established, your Internet traffic emerges without signs of who you are or where you’re connecting from.
If you are considering using a VPN for privacy reasons, check your VPN’s user agreement to see if the provider keeps logs of your online activities. If they do, look for another VPN.
Most VPN services charge for their services; however, there are some free VPN services (they will show ads in your app).
The quality (and privacy policies) of VPN providers varies widely. Search the Internet for current reviews on VPN providers and do some research before selecting one.
The Dark Web & TOR (The Onion Router)

Figure 8.3 The Surface Web, Deep Web & Dark Web
The dark web makes up less than 1% of the web and is designed to provide anonymity for users and website owners. You can’t access the dark web with a normal web browser, you need a special browser – TOR (The Onion Router).
Like the Internet, the core principles behind the TOR network were developed by the US Military. “Onion routing” was designed to protect military intelligence communications online.
The dark web is a popular platform for:
- Those living in countries where they face imprisonment for criticizing their government – journalists, activists, and non-government news agencies.
- Users behind government firewalls who wish to anonymously access information (other than that provided by the state).
- Whistleblowers and information-leakers, for example, Edward Snowden.
- Activists and revolutionaries (like the hacking group Anonymous). The dark web serves as a platform where activists can organize in secret.
- Illegal activities such as drug purchases, stolen credit cards, pirated movies and much more.
The dark web can be a dangerous place for the general internet user, even if they are not involved in any of the illegal activities that occur there. Search the Internet for more information about risks and precautions for the dark web if you intend to access it.
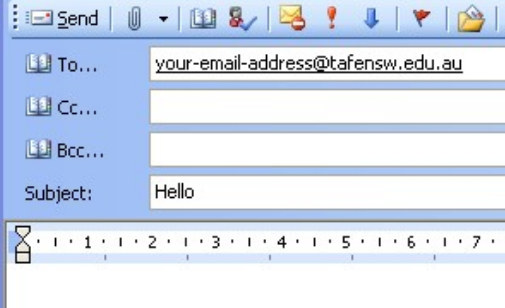
Social Media Privacy Issues
Social media platforms (such as Facebook, LinkedIn, etc.), are websites where you can share details about your life online with family, friends and/or the public.
One of the single biggest issues with social media is that the default privacy settings are typically too broad from a privacy perspective (you end up sharing more details than you expect with a broader audience than you expect).
Details that you make public can be “scraped” (collected using software that simulates a human surfing the web, which then records this information) from these websites without the need to hack into them, as the privacy settings on people’s social media accounts have categorized this data as public rather than private. The use of automated computer programs to do the scraping can result in large amounts of data on many users being available.
In 2021, personal data from 500 million LinkedIn users (about ⅔ of the company’s users) was “scraped” and made for sale online.
Also in 2021, Facebook saw scraped data from about 533 million users posted in an online forum. The data included users: full names, location, email addresses and other information.
In order to protect your privacy, and your personal details so they are not used by a “bad actor” with malicious intent, you can:
limit the audience of your posts (e.g friends only, rather than making them public).
- take a look at your social media platform “settings” and limit how much of your information is made public or shared.
- scale back on details in your profile. For example,
- you can leave out your birth date or your birth year, just provide one piece of that information, not both.
- be careful about adding family members as that information could reveal your mother’s maiden name, which is often used as a security question.
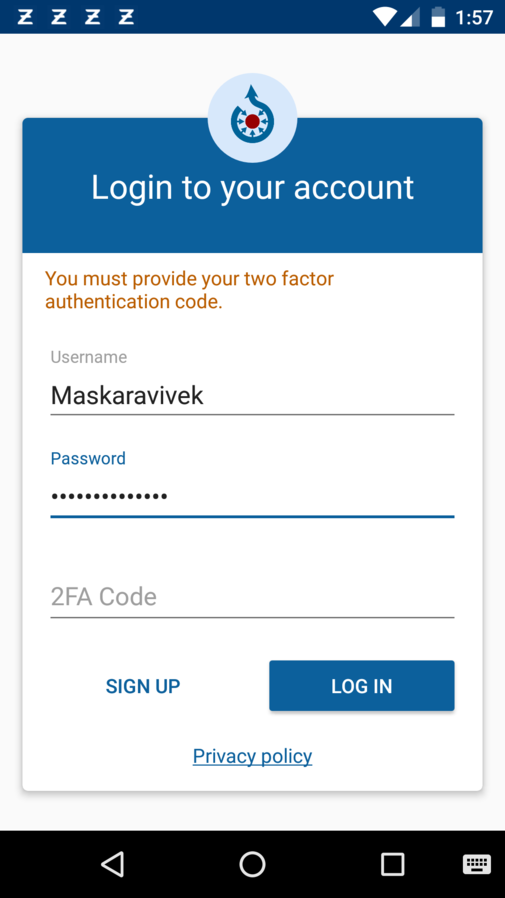
- do not list your mobile phone number publicly, as this phone number is often used in two factor authentication when you log into websites such as your bank, and there are ways in which mobile phone text messages can be intercepted.
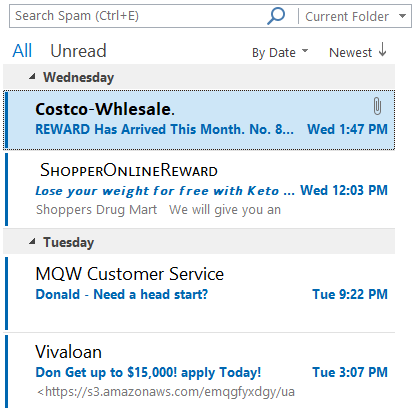
Online Presence
Figure 8.4 It’s a good idea to have a professional online presence.
As part of the hiring process for many companies, the Human Resources (HR) department often surveys the online presence of potential job applicants. There have been numerous instances of the top candidate for a job not being offered the job after their online presence has been searched. It’s prudent for you to search your own name using a search engine, and see what you can find. In order to provide a professional online presence for search engines to find, you may wish to consider:
ePortfolios
Students in college or university may create an ePortfolio during the course of their studies. An ePortfolio is a collection of work (evidence) in an electronic format that showcases learning or accomplishments. It can become a type of enhanced résumé. For example, instead of just saying you write clearly and know how to use software to produce brochures, take a brochure you have produced in class (or at your job) and include that in your ePortfolio. If you don’t already have an ePortfolio, search the words “free ePortfolio” to locate some websites that will allow you to publish one at no charge.
Social Media
If you don’t have a social media presence, potential employers may wonder if your technology skills are lacking, even if you have consciously made the choice not to have one for privacy reasons.
Consider using a professional networking site (such as LinkedIn or others) to establish and maintain professional contacts, and it can also be a way to either find work or further your career. Search for a “LinkedIn tutorial”, to learn how to enhance your online presence.
If you use social media such as Facebook or Twitter, consider having two accounts: one personal, one professional. Reserve the personal account for family and friends, and keep the privacy setting high so that only family and friends can see the posts. With your professional accounts, lower privacy settings could allow a more public view of your posts (which could be beneficial in future job searches), so keep all your posts professional and work-related on this account.
Websites and Blogs
Would you prefer to use a website or blog to project your professional image rather than using social media? There are many free services available, and for a small fee you can register an Internet domain name and host your web site without any advertisements.
Media Attributions