Unit 11. More on electronic communication
Topic C: Web search engine
Click play on the following audio player to listen along as you read this section.
Perform a Search using a Web Search Engine
Search engine – an Internet search engine is a web-based tool (a software) that is designed to search the content of web pages and to find particular information on the Internet.
Some popular search engines
 Google
Google- Bing
- Baidu
- Yahoo!
- Yandex
- Ask.com
- DuckDuckGo
Search the Internet using a web search engine
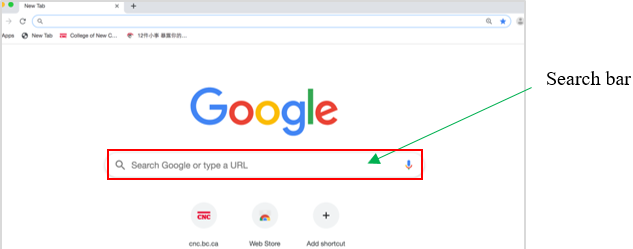
- Open a search engine in a web browser (such as Google in Chrome).
- Type a few specific keywords or phrases to describe whatever you wish to search in the search bar. Search engines look for the keywords in your query.
- Press the Enter key on the keyboard.
- Repeat above steps if necessary.
Security Issues on the Internet
Internet security issues
Although Internet led to many benefits, it also poses a greater potential for security threats.
The common Internet security issues
- Hacker – refers to a person who can gain unauthorized access (break into) to a computer or a network to commit crimes.
- Some things a skilled hacker can do to your computer:
- Hijack your usernames and passwords;
- Gain access to the personal information (credit card numbers, bank account, social insurance number, etc.);
- Steal, change, exploit, sell or destroy data;
- Damage or bring down systems;
- Hold those system hostages to collect ransom.
- Malware (short for malicious software) – a software that is designed to damage, disrupt, or infect computers.
- Malware can gain unauthorized access to a computer and continuously run in the background without owner’s knowledge.
- Malware is a single term that refers to all the different types of threats to your computer safety such as virus, Trojan horse, worm, spyware, etc.
- Computer virus – a specific type of malware that is designed to replicate (copy) and spread from one computer to another.
- A virus can make a copy of itself over and over again.
- A virus can spread from one computer to another through email, removable storage devices, networks (e.g. internet messaging services, download infected files …), etc.
- A virus can damage your computer by corrupting system files, sending spam, stealing data and personal information from your computer, destroying data, deleting everything on your hard drive, etc.
- Trojan horse(or Trojan) – a type of malware that looks harmless but can damage, disrupt, steal data on your computer.
- A Trojan misleads users of its true intent.
- A Trojan may claim to get rid of your computer viruses but instead introduces viruses onto your computer.
- A Trojan can take the form of an innocent-looking email attachment, download, etc.
- Worm – it is similar to a virus (a sub-class of a virus). It is designed to quickly self-replicate and spread copies of themselves from one computer to another.
- The key difference between a virus and a worm is that a virus needs human action to replicate, whereas, a worm doesn’t.
- A virus only spreads when a user opens an affected file whereas a worm spreads without the use of a host file.
- Phishing – a scammer uses deceptive emails or websites and tries to obtain valuable personal information (i.e., username, password, account number, etc.).
- Phishing is a common online scam used by cyber criminals.
- A scammer may use a deceptive email or website appearing to represent a legitimate firm.
 Spyware – a software that secretly monitors (spies) user’s online behavior and gets sensitive information about a person or organization without the user’s knowledge.
Spyware – a software that secretly monitors (spies) user’s online behavior and gets sensitive information about a person or organization without the user’s knowledge.
- A spyware can record a user’s Web browsing habits, e-mail messages, keystrokes on online advertisements, personal information, etc., and forward it to a third party.
- Advertisers can use spyware to target specific advertisements to your tastes.
- Criminal organizations can use spyware to collect financial information (banking accounts, credit card information, password, etc.).
Prevent Cyber Threats
Tips on how to prevent malware from infecting your computer
- Backup files and store in different locations.
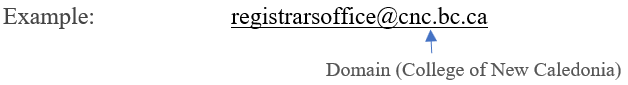
- Don’t open any suspicious / unknown emails or the websites. The second part (the part after the @ ) of an email / website address should represent the company that owns the email / website (domain).
- Don’t download an unknown or a suspicious attachment (document, picture, music, game, video, etc.).
- Do not call fake tech support numbers (tech support scams). If you get pop-up window from fake companies offering to help you with a malware infection, don’t call the number.
- Use a secure and strong password (unique, hard to guess, etc.).
- Install anti-malware / virus software (keep it up to date).
- Scan with antivirus software on a regular basis.

Some free antivirus software:
- Comodo Free Antivirus
- AVAST Free Antivirus
- AVG Antivirus Free
- Avira Antivirus
- Bitdefender Antivirus Free
a web-based tool that is designed to search the content of web pages and find particular information on the Internet.
a person who can gain unauthorized access to (break into) a computer or a network to commit crimes.
a software that is designed to damage, disrupt, or infect computers.
a specific type of malware that is designed to replicate (copy) and spread from one computer to another.
(or Trojan) a type of malware that looks harmless but can cause harm to a computer system.
a type of virus designed to quickly self-replicate and spread copies of itself from one computer to another.
when an Internet scammer uses deceptive emails or websites to try to obtain valuable personal information from people.
a software that secretly monitors (spies) a user’s online behaviour and gets sensitive information about a person or organization without the user’s knowledge.

